When any method from the following table is invoked on a Class, ClassLoader or Thread object, a comparison is run between the method's immediate caller's class loader and that of the object on which the method is invoked.
APIs capable of bypassing SecurityManager's checks |
|---|
|
|
|
|
|
|
|
|
|
|
|
|
|
As an example of what constitutes the immediate caller and the object, consider the method java.lang.Class.newInstance(). Here, the immediate caller is the class that contains this method call whereas the object on which the newInstance() method is being invoked is referred to as the Class object (classObjectName.newInstance()). According to the Java Language Specification [[JLS 2005]], the method getClass() returns the Class object that represents the class of the object.
If a security manager is present, untrusted code that does not have the permissions to use the API directly is prevented from indirectly using trusted code containing the API call to perform the operation. However, the security manager checks are bypassed if the class loader of the immediate caller is the same as or the delegation ancestor of the class loader of the object on which the API is invoked. Consequently, untrusted callers who do not have the required permissions but are capable of passing the class loader check are able to perform sensitive operations if the trusted code invokes these APIs on their behalf.
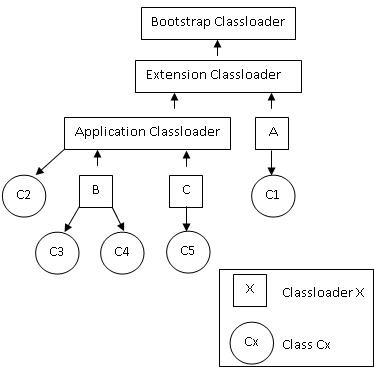
The Java SE 6 class loader delegation hierarchy shown below summarizes several cases and highlights those where security checks are bypassed:
Immediate Caller |
ICC* |
Class Object |
COC** |
Class Loader Check |
Security Check |
|---|---|---|---|---|---|
C1 |
A |
C2, C3, C4, C5 |
Application, B, C |
A is not a delegation ancestor of Application, B or C |
Yes |
C2 |
Application |
C1 |
A |
Application is not a delegation ancestor of A |
Yes |
C2 |
Application |
C3, C4, C5 |
B and C |
Application is a delegation ancestor of B and C |
No |
C3 |
B |
C4 |
B |
The class loader is same for C3 and C4 (B) |
No |
C4 |
B |
C3 |
B |
The class loader is same for C4 and C3 (B) |
No |
C5 |
C |
C1, C2, C3, C4 |
Application, A, B, C |
C is not a delegation ancestor of Application, A, B or C |
Yes |
* ICC: Intermediate caller's class loader
** COC: Class object's class loader
Care must be taken when using these APIs that trusted code does not accept Class objects from untrusted code for further use. For example, if trusted code is loaded by the bootstrap class loader, it can create an instance of a sensitive system class by using the newInstance() method on the Class object. If the method that creates the instance is visible to untrusted code, no security manager checks are carried out to prohibit the untrusted code from indirectly creating the class instance (untrusted code must pass the class loader comparison check).
Similarly, instances of trusted Class objects should not be returned to untrusted code. An untrusted caller can invoke the affected APIs and bypass security checks if its class loader is the same as or the delegation ancestor of the trusted code's class loader.
The table also shows APIs that use the ClassLoader class object. Class loaders facilitate isolation of trusted components from untrusted ones. They also ensure that the untrusted components do not interfere with each other. The proper choice of the class loader to load a class is of utmost importance. Using less trusted class loaders for performing operations of sensitive nature in trusted code can result in vulnerabilities.
With respect to the ClassLoader object APIs, security manager checks may also get bypassed depending on the immediate caller's class loader. Consider for instance, the ClassLoader.getSystemClassLoader() and ClassLoader.getParent() methods that operate on a ClassLoader object. In the presence of a security manager, these methods succeed only if the immediate caller's class loader is the delegation ancestor of the current ClassLoader object's class loader or if the immediate caller's class loader is the same as the current ClassLoader object's class loader or if the code in the current execution context has the getClassLoader RunTimePermission.
As noted earlier, untrusted code can bypass the security checks if its class loader is either the same or a delegation ancestor of the trusted code's class loader. Consequently, care must be taken while specifying the parent of a trusted class loader. Likewise, trusted code should not use a class loader instance supplied by untrusted code. For instance, a class loader instance obtained from untrusted code should not be used to load a trusted class that performs some sensitive operation. Also, a trusted class loader that performs security sensitive operations should never be made available to untrusted code by returning its instance.
Noncompliant Code Example
This noncompliant code example accepts a class object from untrusted code, creates a new instance of the class using the permissions of the immediate caller getInstance() and returns the created instance back to untrusted code.
public class Trusted {
public Object getInstance(Class<?> c) throws InstantiationException, IllegalAccessException {
return c.newInstance();
}
}
Compliant Solution
This compliant solution reduces the accessibility of getInstance() to package-private so that untrusted code cannot obtain the newly created instance.
public class Trusted {
Object getInstance(Class<?> c) throws InstantiationException, IllegalAccessException {
return c.newInstance();
}
}
Noncompliant Code Example
This noncompliant code example shows a vulnerability present in several versions of the Tomcat HTTP web server (fixed in v 6.0.20) that allows untrusted web applications to override the default XML parser used by the system to process web.xml, context.xml and tld files of other web applications deployed on the Tomcat instance. Consequently, untrusted web applications that install a parser can view and/or alter these files under limited circumstances.
This noncompliant code example shows the declaration of a Digester instance in the org.apache.catalina.startup.ContextConfig class. "A Digester processes an XML input stream by matching a series of element nesting patterns to execute Rules that have been added prior to the start of parsing" [[Tomcat 2009]]. The method call chain can be traced as the following:
- The
createWebDigester()method is responsible for creating theDigester. This method internally callscreateWebXMLDigester(). - The method
createWebXMLDigester()requests the methodDigesterFactory.newDigester()to create a new digester instance and sets abooleanflaguseContextClassLoadertotrue. This means that the context class loader, in this case the WebappClassLoader, is used to create the digester.
protected static Digester webDigester = null;
if(webDigester == null){
webDigester = createWebDigester();
}
// This method exists in the class DigesterFactory and is called by ContextConfig.createWebXmlDigester()
// which is in turn called by ContextConfig.createWebDigester()
// webDigester finally contains the value of digester defined in this method
public static Digester newDigester(boolean xmlValidation, boolean xmlNamespaceAware, RuleSet rule) {
Digester digester = new Digester();
// ...
digester.setUseContextClassLoader(true);
// ...
return digester;
}
// Digester.getParser() calls this method. It is defined in class Digester
public SAXParserFactory getFactory() {
if (factory == null) {
factory = SAXParserFactory.newInstance(); // Uses WebappClassLoader
// ...
}
return (factory);
}
- Later, when the
Digester.getParser()method is internally called by Tomcat to process the web.xml and other files, according to the search rules, the parser installed by the untrusted web application is preferred; otherwise, the default parser is used.
The underlying problem is that the newInstance() method is being invoked on behalf of an untrusted web application's class loader.
The Digester class overrides Object's getClassLoader() method and this is used to obtain the class loader to load the class, depending on the value of the flag useContextClassLoader. A partial implementation is shown below.
public ClassLoader getClassLoader() {
// ...
if(this.useContextClassLoader) {
// Uses the context class loader which was previously set to the WebappClassLoader
ClassLoader classLoader = Thread.currentThread().getContextClassLoader();
}
return classloader;
}
Similarly, the contextDigester processing is also broken in the affected versions.
Compliant Solution
This compliant solution uses an init() method to create the webDigester.
protected static Digester webDigester = null;
protected void init() {
if(webDigester == null){
webDigester = createWebDigester();
webDigester.getParser(); // Does not use the context Classloader at initialization
}
// ...
}
The explicit webDigester.getParser() call causes the newInstance() method to be invoked using the container's class loader instead of the WebAppClassLoader. This is because the flag useContextClassLoader is not (??) set during initialization which captures the container's class loader at that time to define the Digester (the context class loader is the container's class loader at this point). Later, even if the Tomcat server still uses the WebappClassLoader to create the parser instance when attempting to process the web.xml and other files, the explicit call to getParser() in init() ensures that the default parser is set during prior initialization and is impossible to replace. Because this is a one-time setting, future attempts to change the parser are futile.
Compliant Solution
Do not accept Class, ClassLoader or Thread instances from untrusted code. If inevitable, safely acquire these instances by ensuring they come from trusted sources. Additionally, make sure to discard tainted inputs from untrusted code. Likewise, objects returned by the affected methods should not be propagated back to the untrusted code.
Note that the Class.newInstance() method requires the class to contain a no-argument constructor. If this requirement is not satisfied, a runtime exception results, which indirectly prevents a security breach.
Risk Assessment
Bypassing Security manager checks may seriously compromise the security of a Java application.
Rule |
Severity |
Likelihood |
Remediation Cost |
Priority |
Level |
|---|---|---|---|---|---|
SEC04-J |
high |
probable |
medium |
P12 |
L1 |
Automated Detection
TODO
Related Vulnerabilities
Search for vulnerabilities resulting from the violation of this rule on the CERT website.
Bibliography
[[CVE 2008]] CVE-2009-0783![]()
[[Gong 2003]] Section 4.3.2, Class Loader Delegation Hierarchy
[[JLS 2005]] Section 4.3.2, "The Class Object"
[[SCG 2007]] Guideline 6-2 Safely invoke standard APIs that bypass SecurityManager checks depending on the immediate caller's class loader
[[Tomcat 2009]] Bug ID 29936![]() , API Class
, API Class org.apache.tomcat.util.digester.Digester, Security fix in v 6.0.20![]()
SEC03-J. Do not allow tainted variables in doPrivileged blocks 14. Platform Security (SEC) SEC05-J. Do not expose standard APIs that use the immediate caller's class loader instance to untrusted code